The compliance automation market is maturing rapidly. The question for most organizations is no longer whether to automate, it's how much can realistically be automated and by whom.
That second part is where most teams run into trouble. Continuous controls monitoring has delivered real value for organizations with the technical depth to implement and maintain it. But for the majority of compliance and security teams who are already stretched thin, already managing an expanding regulatory surface, the dominant tools in the market still require significant specialist involvement to get up and running and more to stay that way.
That's starting to change. Here's how the market has been built, why it has created a skills bottleneck and what a different approach looks like.
The Compliance Team Is Understaffed and Under Pressure
Start with the math. The global cybersecurity workforce gap stands at approximately 4.8 million unfilled roles, with 67% of organizations reporting that they are short on staff. At the same time, the regulatory and certification landscape keeps expanding: NIS2, DORA, the SEC Cybersecurity Disclosure Rule, SOC 2, ISO 27001, PCI DSS. Each new framework brings new requirements, new evidence expectations and new audit cycles.
For compliance managers and security managers, the arithmetic is brutal. More requirements, fewer people, and tools that were designed for specialists. A platform that requires specialist involvement to build or update controls doesn't actually reduce the burden on compliance teams. It just relocates it.
What compliance teams actually need is AI compliance automation that works at their level, not the specialist's level.
Why Most CCM Platforms Still Require a Specialist
Continuous controls monitoring is a powerful concept: instead of periodic audits and manual evidence collection, your controls run automatically against your live environment. Failures surface immediately. Evidence is collected continuously. Compliance posture is visible at all times.
The problem has been how the leading platforms deliver on that promise. The dominant approaches in the market today each represent a meaningful trade-off between coverage and control.
The predefined-domain model. Platforms that offer strong out-of-the-box coverage across predefined control domains—measuring control effectiveness using agentless connectors across your existing security tooling. That's genuinely useful for organizations that need fast time-to-value within those domains. But when your compliance program needs controls that fall outside the predefined model or when you need to build custom controls that reflect your organization's specific policies, you're working within the vendor's structure, configuring rather than authoring. The specialist bottleneck doesn't disappear; it shifts to vendor-mediated customization.
The GRC-first platform. Tools that position CCM as a module within a broader governance, risk and compliance suite. The depth of the platform is real: automated framework mapping, policy management, audit support across a wide range of standards. But the trade-off is implementation complexity. Third-party reviews consistently note a steep learning curve, the need for specialized IT skills or external consultants to configure custom controls and extended timelines when integrating non-standard tooling. These are platforms built for enterprise GRC teams with dedicated technical resources, not for the security and compliance manager who needs to stand up a new control program this quarter.
The service-wrap model. Vendors that offer CCM platforms combined with managed implementation services, their "CCM Unique Service Wrap" engages their team directly in standing up and maintaining the control environment. For organizations that want a supported onboarding experience, that model has real advantages. But it also means the compliance team is dependent on vendor engagement to build, modify and expand their control library. The team is the beneficiary of the program, not the operator of it.
Each of these approaches solves real problems. None of them makes continuous controls monitoring something a security or compliance team can own and evolve independently.
Why Generic AI Doesn't Close the Gap
The past two years have produced a wave of "AI-assisted" compliance features across the market. Most of them share a common limitation: the AI is generic. It can suggest language, auto-complete fields or summarize findings but it's working without context. It doesn't know what requirement you're trying to satisfy. It doesn't know which framework you're operating under. It doesn't understand the specific control objective your team is trying to enforce.
When AI is added as a feature layer on top of a complex or constrained architecture, it speeds up specialist work. It doesn't change who can do the work. You still need someone who understands the underlying control model, knows what a well-formed test looks like and can evaluate whether the AI's output is actually correct.
Context-aware AI is a different proposition entirely. When the AI understands the specific requirement it's working against: the framework, the control objective, the intended test logic, it produces suggestions that are meaningfully more accurate and actionable. The gap between "AI helped me type faster" and "AI helped me build something I couldn't have built myself" is the gap between generic assistance and context-aware authoring.
That distinction matters most for the compliance manager and security manager who don't have an engineering background. For them, generic AI is a faster onramp to the same wall. Context-aware AI changes what's possible.
What This Looks Like in Practice: A Five-Minute Control
Here's a concrete example. Suppose your team needs to verify that all S3 buckets in your AWS environment have encryption enabled—a common requirement under CIS AWS Foundations and internal data protection policies.
On a platform that requires manual query authoring or specialist configuration, standing up this control requires a security engineer to write the query logic, validate it against your integration data, confirm the test type is correct and run it through whatever approval process exists before it affects your compliance posture. That process might take days to schedule, hours to execute and another review cycle to clear.
With context-aware AI compliance automation, the flow looks like this:
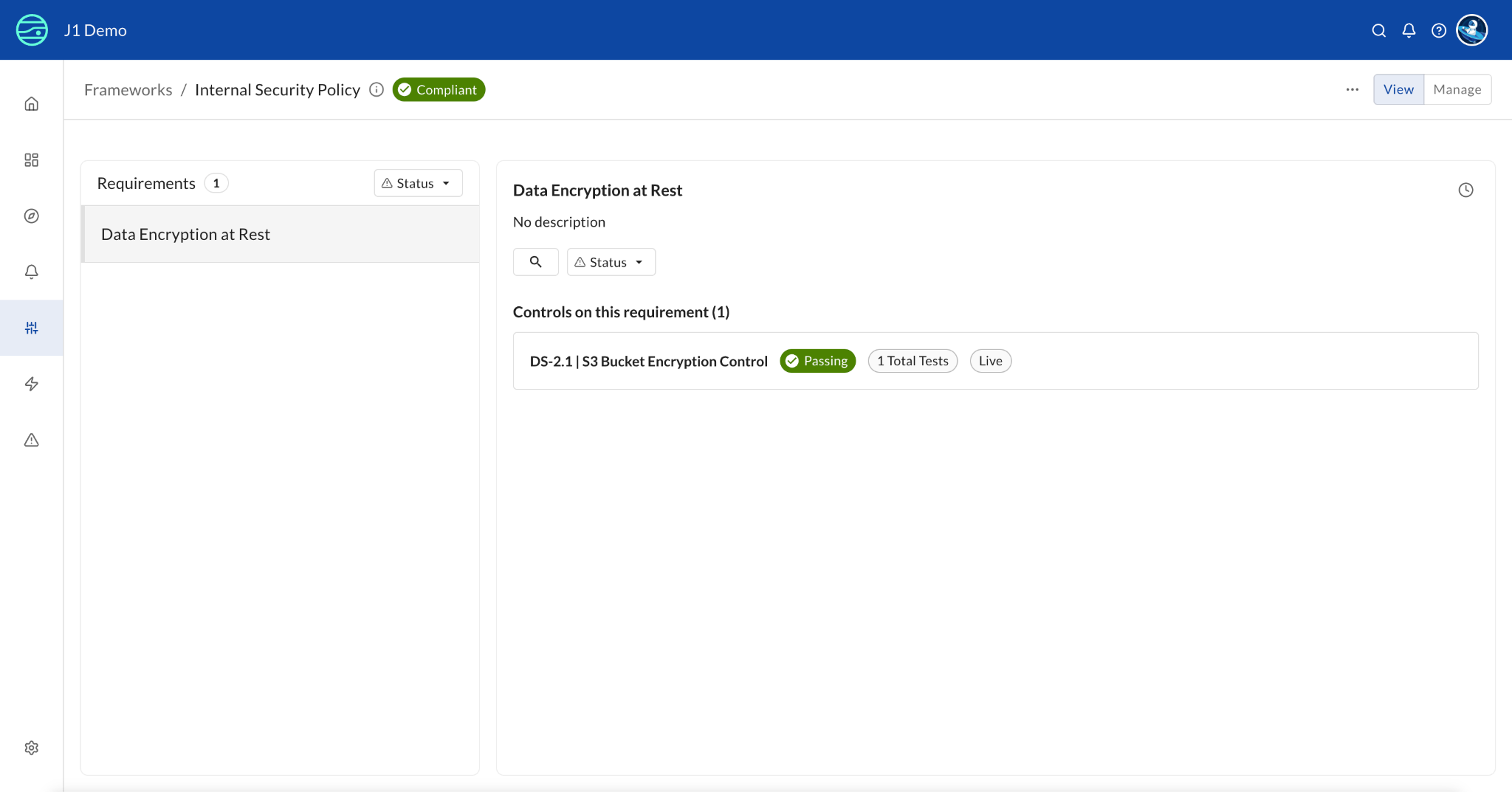
Step 1 — Create your framework and requirements in the UI. No JSON imports. No schema knowledge required. A compliance manager opens the interface, creates a framework called "Internal Security Policies," adds a requirement ("All S3 buckets must have encryption enabled"), and saves it. The entire structure exists in the platform without writing a single line of code.
Step 2 — Create a control using AI-assisted authoring. From the requirement, you click "Create Control" and enter a title: "S3 Bucket Encryption Control." The AI, which already has context from the linked requirement, auto-populates a description, remediation steps and a severity rating. Not generic boilerplate. Content that reflects what this specific control is meant to enforce.
Step 3 — Add a control test. The AI writes the query. You select test type "BAD" (returning non-compliant resources), enter a plain-English title ("S3 buckets without encryption enabled"), and watch the AI generate the query:
FIND aws_s3_bucket WITH encrypted != false
You click "Preview Results" to see the actual entities returned, confirm the query is working against your live data and save. The platform tells you which integrations this test depends on, eliminating the "why isn't my control working?" mystery that plagues manual configurations.
Step 4 — Govern it. The control saves in Draft state. You move it to Review for a colleague to validate, then to Live. Only Live controls affect your compliance posture—untested logic never makes it into your active program.
The whole process: under five minutes. No specialist required. No vendor engagement needed.
What Changes for Your Team
The operational shift here is significant. When compliance automation no longer requires specialist involvement, the compliance manager and security manager become the primary operators of the program and not just consumers of its output.
That means faster control coverage, because you're not waiting on engineering backlogs or vendor service queues. It means broader organizational participation, because control owners across the business can engage directly. And it means a more accurate compliance program, because the people who best understand the regulatory requirements are now the ones building and governing the controls.
The governance model matters here too. A formal lifecycle—Draft, Review, Live, Retired—ensures that no untested control affects your compliance posture. Every state transition is logged. Your auditors get a clean history of how controls were developed and approved. That's compliance infrastructure that your compliance team owns and operates independently.
The Accessible Path to Continuous Controls Monitoring
The fundamental value of continuous controls monitoring—always-on visibility, automated evidence collection, real-time failure detection—has never been in question. The established platforms in the market deliver real value for organizations that have the technical depth to configure and maintain them.
What's been missing is accessibility. When AI compliance automation is context-aware rather than generic, when the platform is built for the compliance team rather than the specialist and when governance is built into the workflow rather than managed through vendor services, CCM becomes what it was always supposed to be: a program your whole team can run.
The compliance automation market has matured. The question now is whether the tool you choose empowers your team to operate it or just benefits them while someone else does.
See how JupiterOne CCM delivers AI compliance automation without coding. Request a demo →







.png)

