Identity and Access Management
Discover and prioritize IAM risks across all your assets
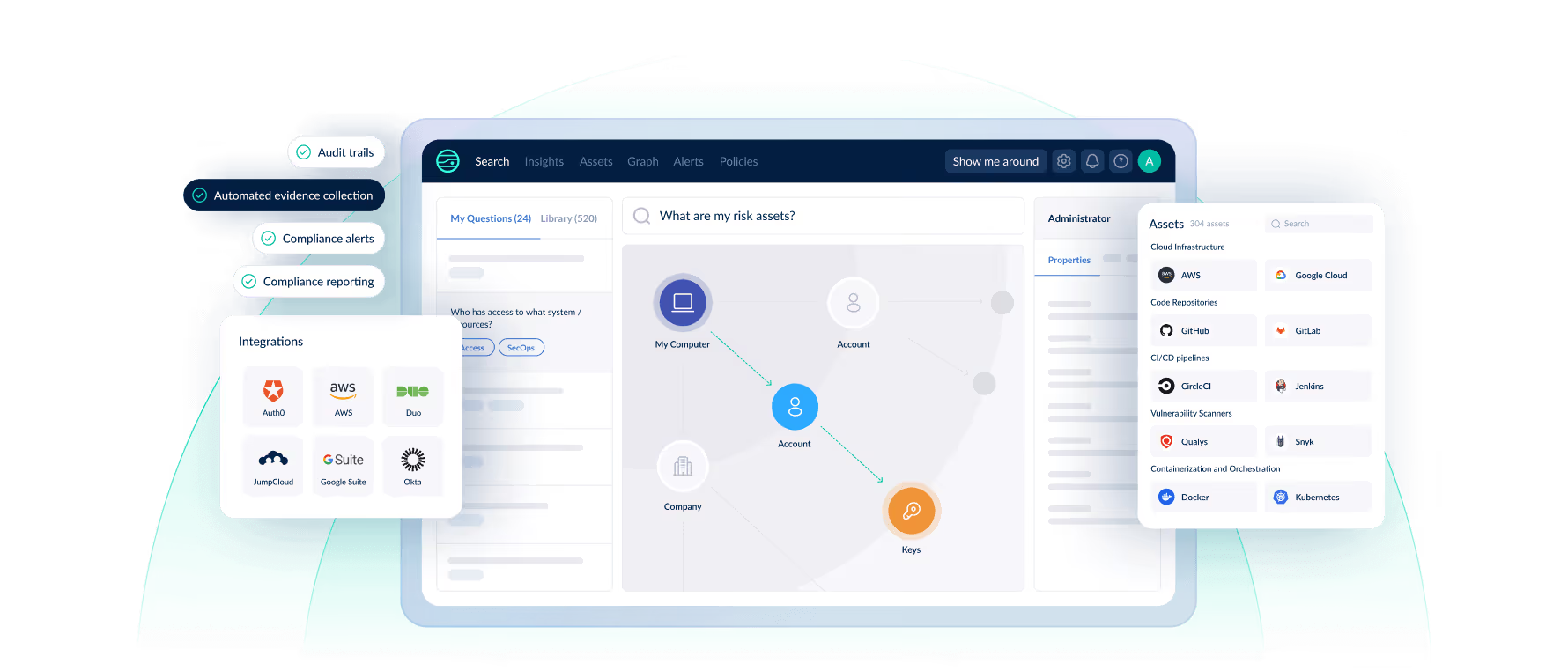
Get a complete inventory of user identities. See who has access to what systems and resources. Automate user access reviews, and identify permissions, entitlement, and misconfiguration issues.
Get a Demo


Why Identity and Access Management
Security Teams Cannot Protect Their Org Without a Complete Understanding of User Identities
Teams often don’t have a centralized inventory of their user identities and permissions. This makes it hard to pinpoint user- and access-driven vulnerabilities, see which assets are at risk, and secure your attack surface.
JupiterOne centralizes user identity data to automate access reviews, identify permission issues, and spot misconfigurations.
How it works

Consolidate IAM data
Clear Visibility
View all identities and permissions across your cloud assets, users, devices, code repos, and apps. Identify unknown or unauthorized privileges.

Identify permission issues
Prioritize Critical Risks
See the blast radius of security incidents. Identify the connections between user identities, threats, and business critical assets. Prioritize risks.

Remediate faster
Increase Environment Compliance
Get recommended remediation steps. Increase compliance for security frameworks, like NIST, ISO, CIS, SOC 2, and PCI-DSS. Streamline audits.





































