In this "Bite-size Security Showcase", Erich Smith walks through a common developer security scenario, dealing with vulnerable third party dependencies. Specifically, Erich takes a look at NPM packages.
Staying updated with NPM dependencies requires automation. In this video example, Erich examines a situation where automated PRs are not available, but the build needs to be quickly remediated. He works through how to update the vulnerable packages on the command-line using YARN, starting with a local sanity check, and then moves through updating to the latest version of the packages containing security fixes. He runs a quick "git dif" against the package json to see the impact of the changes.
A deep transitive dependency is then explored, including the use of "npx-yarn-audit-fix", a conversion wrapper around the npm-audit-fix process.
This all leads to a security best practice: clean as you go. Don't wait for your project to fail in CI/CD due to dependency vulnerabilities. Work with your team to process your Dependabot PRs in a timely fashion, and make liberal use of YARN audit throughout your day-to-day development cycle. Finally, update packages when it's convenient for you, not under stress.
Other Resources:
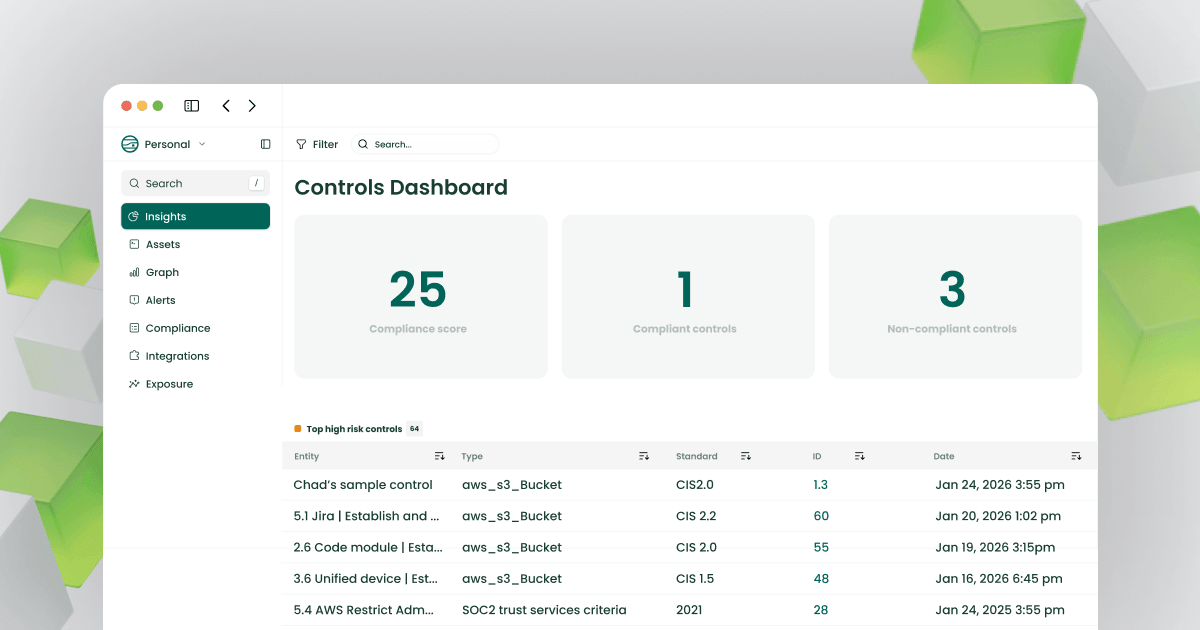
- Video: Managing GRC with JupiterOne
- Video:J1 Query to Expose (Un)approved AMIs Interrogate Your AWS Env
- Community Video Gallery and Downloadable Resources
- Free J1 Environment






.jpg)
